At 8:30 in the evening on Wednesday 2 November 1988, a 23-year-old graduate student named Robert Tappan Morris, in his first semester of a PhD programme in computer science at Cornell University, logged into a Massachusetts Institute of Technology computer fr…
At 8:30 in the evening on Wednesday 2 November 1988, a 23-year-old graduate student named Robert Tappan Morris, in his first semester of a PhD programme in computer science at Cornell University, log… [+7846 chars]
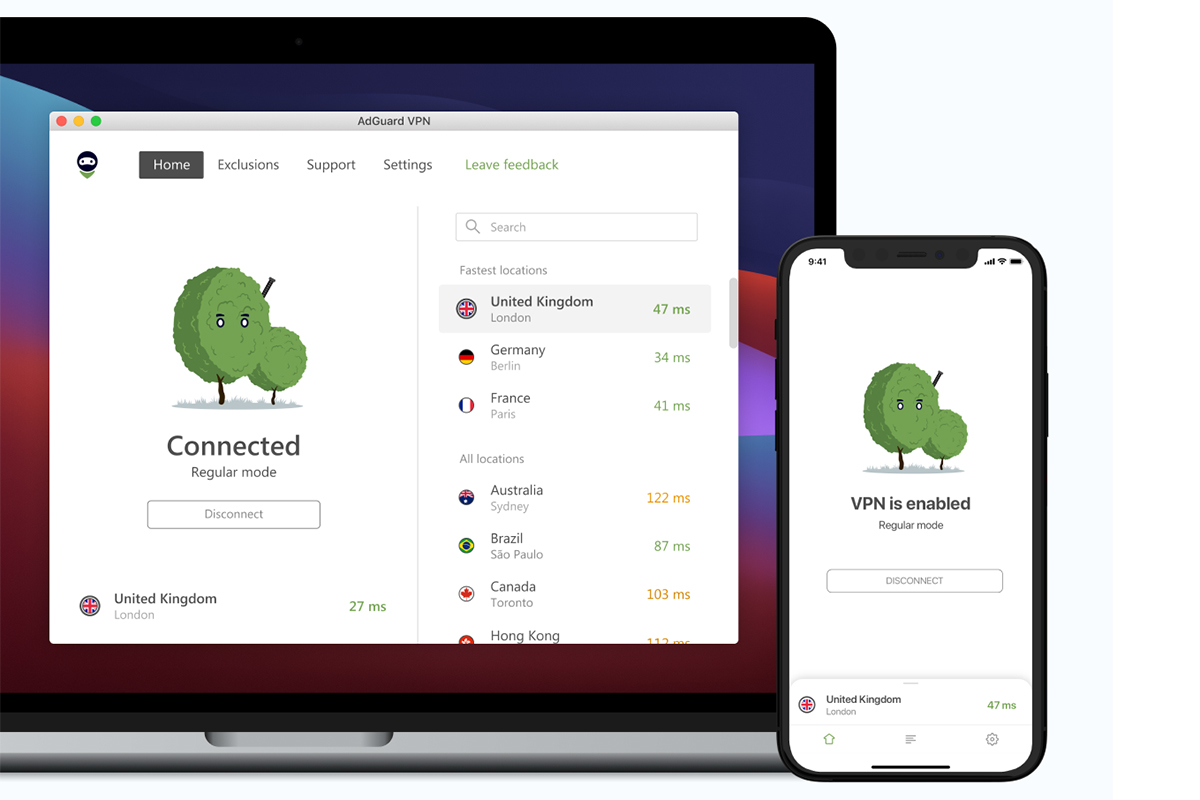
Fast, private browsing and family-wide protection in one discounted bundle.
The post Safeguard your family with AdGuard VPN & the Security Suite for $35 appeared first on Popular Science.
We may earn revenue from the products available on this page and participate in affiliate programs. Learn more TL;DR: AdGuard VPN and the Family Plan provide a combined approach to online safety, so … [+2430 chars]
Spending extra on a good VPN service is a net benefit that’ll always pay off in the backend. But with this $49.99 (reg. $89.95) 1-year subscription to the ExpressVPN Advanced Plan, you can cut costs without any of the fallout. Better yet, your subscription gi…
Spending extra on a good VPN service is a net benefit thatll always pay off in the backend. But with this $49.99 (reg. $89.95) 1-year subscription to the ExpressVPN Advanced Plan, you can cut costs w… [+2454 chars]
Ciena reports blockbuster fiscal Q2 but stock slumpsSK Telecom joins Anthopic’s Project GlasswingFoxconn gets jiggy with Intel and SK Group
In today’s industry news roundup: Despite beating sales and margin expectations and raising its annual revenues forecast, Ciena’s stock has dropped off a cliff; SK Telecom becomes the latest telco to… [+7979 chars]
“In the age of misinformation, the line between fact and fiction is blurrier than ever.” “For those of us working in video news, verification isn’t a nice-to-have. It’s a necessity. It is how we protect the stories we help shape and how we earn and maintain t…
“In the age of misinformation, the line between fact and fiction is blurrier than ever.
For those of us working in video news, verification isnt a nice-to-have. Its a necessity. It is how we protect… [+14334 chars]
The digital threats faced by defenders of truth and democracy are multiplying. So should the capacity to respond to them. Through tools like Ricochet Refresh and cybersecurity training across lower- and middle-income countries, Blueprint for Free Speech helps…
++ This guest post is part of a spotlight series on the organizations defending the free Internet.++
Fear of digital surveillance breeds silence.
In the words of a youth activist in Zambia who t… [+6597 chars]
Tern Orox Technology Shines with the Bosch Flow App It turns out the Tern Orox into something more than an eBike. The Tern Orox is…
The post Tern Orox Technology Shines appeared first on Bike Hugger.
It turns out the Tern Orox into something more than an eBike. The Tern Orox is already one of the most interesting bikes on the market. Its a cargo bike, an adventure bike, a car replacement, and a b… [+4540 chars]
MUMBAI, India, June 03, 2026 (GLOBE NEWSWIRE) -- Fairplay today announced the implementation of an enhanced user verification framework and updated account security measures designed to align with India's evolving 2026 online gaming regulatory requirements. T…
MUMBAI, India, June 03, 2026 (GLOBE NEWSWIRE) -- Fairplay today announced the implementation of an enhanced user verification framework and updated account security measures designed to align with In… [+5531 chars]
Forget about email hackers. What if someone nabs your external drive and all the data on it? Thwart thieves with a drive with strong encryption and security features. We've tested loads of them.
A Guide to Hardware-Based Drive EncryptionEncryption is the proc…
It could be an accident, it could be theft: It's just too easy for the data on an unsecured external hard drive or SSD to fall into the wrong hands. To keep your data safe, consider an encrypted exte… [+8227 chars]
French President Emmanuel Macron has looked to win over tech bosses amid hopes to boost AI capability.
OpenAI chief Sam Altman will be attending the G7 conference in France later this month, CNBC has learned, as President Emmanuel Macron steps up efforts to court tech leaders across the globe in suppo… [+3021 chars]
Public skill marketplaces are being flooded with malicious skills that steal credentials, exfiltrate data, and hijack agents. In response, a segment of the security industry released skill scanners, a new family of tools designed to detect malicious skills be…
Public skill marketplaces are being flooded with malicious skills that steal credentials, exfiltrate data, and hijack agents. In response, a segment of the security industry released skill scanners, … [+19867 chars]
Anthropic had announced on Tuesday that it gave approximately 150 organisations around the world access to its AI model Mythos, whose ability to rapidly identify weaknesses in computer security has sparked global concern about vulnerabilities.
Claude-maker Anthropic said it will provide access to its powerful Mythos model to companies and institutions in more than 15 countries, including India, the Financial Times reported.Anthropic had an… [+1285 chars]
Working with AI world leaders at CommBank’s San Francisco Tech Hub offers CommBank’s technologists the opportunity to learn at the frontier in the world’s leading technology ecosystem.
Technologists at the new San Francisco Tech Hub learn from partners such as OpenAI and Anthropic to support adoption of emerging AI technologies. It builds on CommBank’s Seattle Tech Hub, where more … [+5694 chars]
Anthropic has opened access to its new AI model, Mythos, to 150 organisations worldwide. This powerful AI can rapidly find computer security flaws. Early tests revealed thousands of vulnerabilities. Now, groups from over 15 countries, including critical infra…
Anthropic on Tuesday gave approximately 150 organisations around the world access to Mythos, its powerful new AI model whose rapid ability to identify weaknesses in computer security that has sparked… [+2372 chars]
Buddhist fundamentalism functions in post-coup Myanmar not as a parallel force to military authoritarianism, but as an integral component of it.
In February 2026, Myanmars widely condemned sham general elections received a public endorsement from Ashin Wirathu, the founder of religious fundamentalist movements 969 and Ma Ba Tha and a figure l… [+10754 chars]
I’m not saying Windows is a terrible operating system, but it’s definitely no longer the one I choose to use on a day-to-day basis.
After 30+ years of using Windows in its various forms (starting with Windows 95), I have moved on — but not to macOS! In …
Skip to contentType your search and hit enter
When you purchase through links in our articles, we may earn a small commission. This doesn't affect our editorial independence
.
I’m not saying Windo… [+9722 chars]
However, the US-Israel security partnership is no longer confined to conventional security cooperation.
Recently, both Israel and the US have made huge strides in areas such as cybersecurity, artificial intelligence, missile defense, drones, and also border security, among others. Such cooperation will… [+5560 chars]
Archives (PRELIMS Focus) (MAINS Focus)
The post DAILY CURRENT AFFAIRS IAS | UPSC Prelims and Mains Exam – 29th May 2026 appeared first on IASbaba.
GS Paper III Science & Technology (Cyber Security) | GS Paper III SecurityQuantum Computing; Post-Quantum Cryptography (PQC); Quantum Key Distribution (QKD); Digital Infrastructure Protection
In… [+6732 chars]
AI on the Lot, which has grown from a half-day conference for 600 in 2023 to a two-day draw for nearly 2,500, delivered another dose of techno-optimism this year. Hollywood, however, still has reservations. Amazon MGM Studios hosted the event on its Culver Ci…
AI on the Lot, which has grown from a half-day conference for 600 in 2023 to a two-day draw for nearly 2,500, delivered another dose of techno-optimism this year. Hollywood, however, still has reserv… [+6616 chars]
Peter G. Neumann, former Principal Scientist in SRI’s Computer Science Laboratory, passed away this week after decades as one of computing’s most principled and far-sighted voices. He joined SRI as a computer scientist in 1971.Dr. Neumann dedicated his career…
Peter G. Neumann, former Principal Scientist in SRI’s Computer Science Laboratory, passed away this week after decades as one of computing’s most principled and far-sighted voices. He joined SRI as a… [+566 chars]
Amnesty International Nigeria trains 30 young human rights defenders in Cross River to strengthen civic space and promote human rights awareness at the gra
Read More: https://punchng.com/amnesty-trains-30-youths-to-defend-human-rights-in-cross-river/
Amnesty International Nigeria has trained 30 young human rights defenders in Cross River State as part of efforts to strengthen civic space protection and promote human rights awareness at the grassr… [+4088 chars]
The Morphing Paradigm LAST UPDATED: May 29, 2026 at 5:06 PM GUEST POST from Art Inteligencia I. Introduction: Beyond the Flat Screen and the Static Prototype The Hook: For decades, innovators and experience designers have been trapped in two dimensions (scree…
The Morphing Paradigm
LAST UPDATED: May 29, 2026 at 5:06 PM
GUEST POST from Art Inteligencia
I. Introduction: Beyond the Flat Screen and the Static Prototype
The Hook: For decades, innovators and… [+13755 chars]
Cyberattack outages don’t just disrupt access; they reshape our relationship with technology. Case studies like Canvas and La Poste show how downtime halts education and commerce, while official status pages often stay vague. That’s where Status Is Down matte…
Weve all been thereyou refresh a page, get a spinning wheel of death, and sigh. Most of the time, digital outages are just minor speed bumps. A server gets overloaded, a routine update goes sideways,… [+6649 chars]
The new direction reflects how online threats have evolved beyond malicious files to phishing, scams, identity theft, and account takeover The new direction reflects how online threats have evolved beyond malicious files to phishing, scams, identity theft, an…
NEW YORK, May 29, 2026 (GLOBE NEWSWIRE) -- NordVPN today announces that it is bringing its next-generation antivirus
capabilities to the forefront alongside its VPN, reflecting how digital threats … [+3742 chars]
USISPF said Goyal provided an “encouraging update on US-India trade negotiations, assuring the industry that an interim agreement is close"
Commerce and Industry Minister Piyush Goyal gave assurances that the India-US interim agreement is close as he provided an encouraging update on bilateral trade negotiations during an interaction wit… [+4228 chars]